



Salesforce-MuleSoft-Developer-II Exam Questions With Explanations
The best Salesforce-MuleSoft-Developer-II practice exam questions with research based explanations of each question will help you Prepare & Pass the exam!



Over 15K Students have given a five star review to SalesforceKing



Why choose our Practice Test
By familiarizing yourself with the Salesforce-MuleSoft-Developer-II exam format and question types, you can reduce test-day anxiety and improve your overall performance.
Up-to-date Content
Ensure you're studying with the latest exam objectives and content.
Unlimited Retakes
We offer unlimited retakes, ensuring you'll prepare each questions properly.
Realistic Exam Questions
Experience exam-like questions designed to mirror the actual Salesforce-MuleSoft-Developer-II test.
Targeted Learning
Detailed explanations help you understand the reasoning behind correct and incorrect answers.
Increased Confidence
The more you practice, the more confident you will become in your knowledge to pass the exam.
Study whenever you want, from any place in the world.

Salesforce Salesforce-MuleSoft-Developer-II Exam Sample Questions 2025
Start practicing today and take the fast track to becoming Salesforce Salesforce-MuleSoft-Developer-II certified.
2604 already prepared
Salesforce Spring 25 Release60 Questions
4.9/5.0
Refer to the exhibit.
What is the result if ‘’Insecure’’ selected as part of the HTTP Listener configuration?
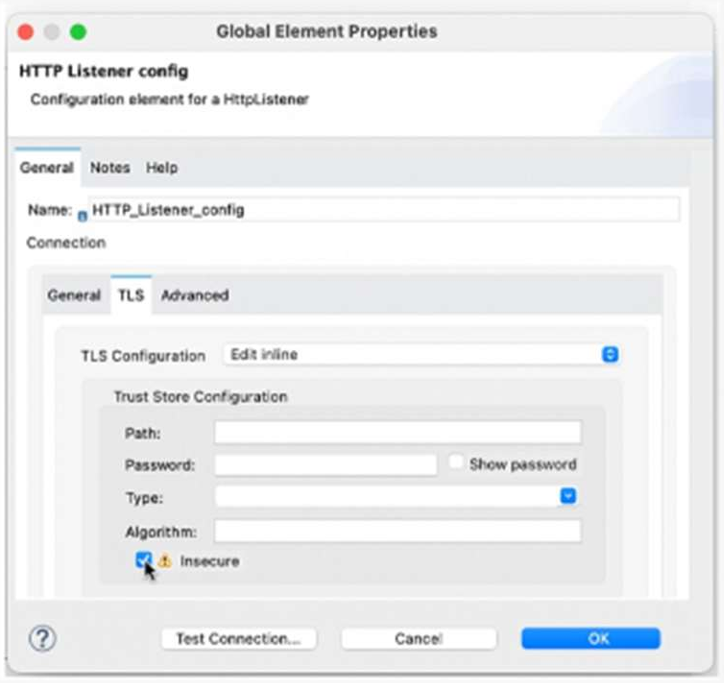
A. The HTTP Listener will trust any certificate presented by the HTTP client
B. The HTTP Lister will accept any unauthenticated request
C. The HTTP listener will only accept HTTP requests
D. Mutual TLS authentication will be enabled between this HTTP Listener and an HTTP client
Explanation:
When configuring an HTTPS Listener in MuleSoft, enabling the “Insecure” checkbox means:
The listener does not validate the client’s certificate.
It accepts any certificate, even if it’s self-signed, expired, or from an untrusted CA.
This is typically used in development or testing environments, where strict TLS validation is not required.
Why the Other Options Are Incorrect:
B. Accepts any unauthenticated request
Not accurate — it still uses HTTPS, just skips certificate validation.
C. Only accepts HTTP requests
Incorrect — “Insecure” applies to HTTPS, not HTTP.
D. Mutual TLS authentication enabled
Opposite — “Insecure” disables certificate validation, which is required for mutual TLS.
Reference:
You can read more about this in the MuleSoft HTTP Listener Configuration Guide.
Would you like to explore how to securely configure mutual TLS in MuleSoft for production environments?
An API has been built to enable scheduling email provider. The front-end system does very
little data entry validation, and problems have started to appear in the email that go to
patients. A validate-customer’’ flow is added validate thedata.
What is he expected behavior of the ‘validate-customer’’ flow?
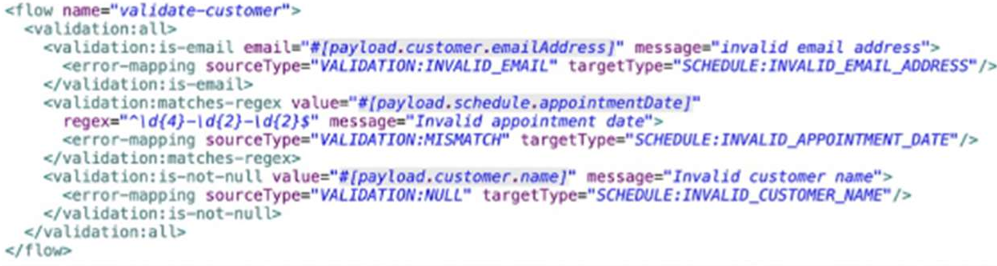
A. If only the email address Is invalid a VALIDATION.INVALID_EMAIL error is raised
B. If the email address is invalid, processing continues to see if the appointment data and customer name are also invalid
C. If the appointment date and customer name are invalid, a SCHEDULE:INVALID_APPOINTMENT_DATE error is raised
D. If all of the values are invalid the last validation error is raised:SCHEDULE:INVALID_CUSTOMER_NAME
Explanation:
This question is testing your understanding of error handling and validation flow within Mule applications, specifically how validation components typically behave and how errors are propagated.
Let's break down the options:
A. If only the email address Is invalid a VALIDATION.INVALID_EMAIL error is raised
Plausible. In a typical validation flow, if a specific validation rule fails (e.g., email format), an error related to that failure is raised immediately. This is standard behavior for "fail-fast" validation.
B. If the email address is invalid, processing continues to see if the appointment data and customer name are also invalid
Less plausible for a single validate-customer flow designed for "fail-fast". While you can design validation to collect all errors before throwing, a single validate-customer flow implies a sequence. If the email is fundamentally invalid, continuing to validate other fields for the same customer might be redundant if the overall record is already considered invalid. However, if the validate-customer flow contains multiple, independent validation components that are designed to execute regardless of prior failures (e.g., using a scatter-gather for parallel validation, or a custom approach), this could happen, but it's not the most common "expected behavior" for a named validation flow unless explicitly stated.
C. If the appointment date and customer name are invalid, a
SCHEDULE:INVALID_APPOINTMENT_DATE error is raised
Highly Unlikely. If multiple validation errors occur within a sequential flow, typically only the first error encountered will be propagated and stop the flow, unless there's specific logic to aggregate errors. If both the appointment date and customer name are invalid, and the validation for appointment date precedes customer name, then SCHEDULE:INVALID_APPOINTMENT_DATE would be raised. However, if the customer name validation precedes the appointment date, then SCHEDULE:INVALID_CUSTOMER_NAME would be raised. This option implies a specific priority, but not the general behavior when multiple validations fail sequentially.
D. If all of the values are invalid the last validation error is raised:
SCHEDULE:INVALID_CUSTOMER_NAME
Plausible if validations are sequential and CUSTOMER_NAME is the last one checked. This aligns with the "fail-fast" principle where the first encountered error stops the flow and is raised. If CUSTOMER_NAME validation is the last one in sequence and all previous ones passed (or were not reached because of an earlier failure), and then CUSTOMER_NAME fails, this would be the error raised. However, the question implies multiple validations within the validate-customer flow. If the first validation (e.g., email) fails, then subsequent validations for appointment date and customer name might not even be executed.
Re-evaluating based on "Expected Behavior"
In a typical MuleSoft validation scenario, especially with out-of-the-box validation components:
Fail-Fast is the
default: When a validation component encounters an invalid input, it typically stops further processing in that path and raises an error immediately.
Error Type Specificity: The error raised will usually be specific to the validation that failed.
Given this, let's reconsider:
If the validate-customer flow is designed to validate sequentially (email, then appointment date, then customer name):
If the email is invalid, it would raise an INVALID_EMAIL error and stop.
If the email is valid but the appointment date is invalid, it would raise an INVALID_APPOINTMENT_DATE error and stop.
If both email and appointment date are valid but the customer name is invalid, it would raise an INVALID_CUSTOMER_NAME error and stop.
Now, let's look at the options again with this understanding:
A. If only the email address Is invalid a VALIDATION.INVALID_EMAIL error is raised
This is the most accurate description of typical "fail-fast" validation behavior. If the email is the first validation to fail, it will be the error that's raised, and subsequent validations won't be performed.
B. If the email address is invalid, processing continues to see if the appointment data and customer name are also invalid
This would only happen if the validation flow is explicitly designed for all-at-once validation (e.g., using a custom aggregator or All scope with specific error handling to collect all errors). This is not the default or "expected" behavior of a simple validation flow.
C. If the appointment date and customer name are invalid, a SCHEDULE:INVALID_APPOINTMENT_DATE error is raised
This is too specific and assumes the order of validation and that the SCHEDULE:INVALID_APPOINTMENT_DATE is always the first one to fail among those two. It doesn't account for the email validation potentially failing first.
D. If all of the values are invalid the last validation error is raised: SCHEDULE:INVALID_CUSTOMER_NAME
This is only true if the customer name validation is the last one in the sequence and all preceding validations passed. If "all values are invalid," the first invalid value encountered in the sequence would typically cause the error to be raised, not necessarily the last one.
Conclusion:
The most standard and "expected" behavior of a validation flow in MuleSoft, especially when not specified otherwise (like collecting all errors), is to fail fast. This means the moment an invalid condition is met, an error specific to that condition is raised, and the flow stops.
Therefore, if the email address is the first thing validated and it's invalid, that's the error that will be raised.
The final answer is
A
A developer is working on a project that requires encrypting all data before sending it to a backend application. To accomplish this, the developer will use PGP encryption in the Mule 4 Cryptography module. What is required to encrypt the data before sending it to the backend application?
A. The application needs to configure HTTPS TLS context information to encrypt the data
B. The application needs to both the private and public keys to encrypt the data
C. The application needs the public key from the backend service to encrypt the data
D. The application needs the private key from the backend service to encrypt the data
Explanation:
In PGP (Pretty Good Privacy) encryption, the standard mechanism is:
➝ Public key is used to encrypt the data.
➝ Private key is used to decrypt the data.
Since the backend application is the receiver, it must own the private key and share the public key with the Mule app (sender). The Mule app uses the public key to encrypt data, and only the backend can decrypt it using its private key.
This ensures:
➝ Confidentiality (only the intended receiver can decrypt).
➝ No private key is ever exposed.
❌ Why the other options are wrong:
A. The application needs to configure HTTPS TLS context information to encrypt the data
🔸 Incorrect: TLS is used for transport-level encryption, not PGP data-level encryption. This doesn’t meet the requirement of encrypting all data before sending.
B. The application needs both the private and public keys to encrypt the data
🔸 Incorrect: Only the public key is needed to encrypt. Private key is only needed for decryption and must remain secret with the receiver (backend).
D. The application needs the private key from the backend service to encrypt the data
🔸 Incorrect: Sharing the private key is a security risk. The sender should never need or have access to the backend’s private key.
🔗 Reference:
MuleSoft Docs → Cryptography Module - PGP
Official MuleSoft Encryption Guide → Using PGP Encryption in Mule 4
Which pattern should be used to invoke multiple HTTP APIs in parallel and roll back failed requests in sequence?
A. A database as a transactional outbox and an Until Successful router to retry any requests
B. A Parallel for Each scope with each HTTP request wrapped in a Try scope
C. Scatter-Gather as central Saga orchestrator for all API request with compensating actions for failing routes
D. VM queues as a reliability pattern with error handlers to roll back any requests
Explanation:
✅ Correct Answer: C. Scatter-Gather as central Saga orchestrator for all API requests with compensating actions for failing routes
The Scatter-Gather component in MuleSoft is ideal for invoking multiple HTTP APIs in parallel, as it sends requests concurrently and collects responses. To handle rollbacks in sequence, Scatter-Gather can act as a central Saga orchestrator, a pattern where each API request is treated as a step in a distributed transaction. If any request fails, compensating actions (e.g., calling a rollback endpoint or reversing the action) are executed in sequence for the failed routes. This ensures that partial failures are undone systematically, maintaining consistency across APIs. MuleSoft’s documentation on Scatter-Gather and the Saga pattern (in API-led connectivity) highlights its use for parallel processing with compensating transactions to manage distributed rollbacks.
❌ Incorrect Answers:
❌ A. A database as a transactional outbox and an Until Successful router to retry any requests
The transactional outbox pattern involves storing API requests in a database and processing them reliably, often with retries via an Until Successful router. While this ensures reliability, it does not support parallel invocation of multiple APIs, as requests are typically processed sequentially. Additionally, the outbox pattern focuses on eventual consistency rather than sequential rollbacks with compensating actions. MuleSoft’s documentation on the outbox pattern notes its use for reliable message delivery, not parallel API calls with orchestrated rollbacks.
❌ B. A Parallel For Each scope with each HTTP request wrapped in a Try scope
The Parallel For Each scope in MuleSoft executes iterations concurrently, which could invoke multiple HTTP APIs in parallel. Wrapping each request in a Try scope allows error handling for individual failures. However, Parallel For Each does not provide a centralized mechanism to orchestrate sequential rollbacks across all APIs, as required by the Saga pattern. Managing compensating actions would require complex custom logic, making it less suitable than Scatter-Gather. MuleSoft’s documentation on Parallel For Each indicates it’s designed for independent parallel processing, not coordinated distributed transactions.
❌ D. VM queues as a reliability pattern with error handlers to roll back any requests
Using VM queues in MuleSoft ensures reliable message delivery by persisting requests in intra-application queues, with error handlers to manage failures. However, VM queues process messages sequentially or require multiple queues for parallelism, which lacks the centralized coordination needed for parallel API invocations and sequential rollbacks. Compensating actions for rollbacks would need additional custom orchestration, unlike the Scatter-Gather Saga approach. MuleSoft’s VM Connector documentation emphasizes reliability for asynchronous processing, not parallel API orchestration with rollback coordination.
🧩 Summary:
Option C is correct because Scatter-Gather supports parallel HTTP API invocations and can act as a Saga orchestrator to execute compensating actions in sequence for failed requests. Options A (outbox with retries), B (Parallel For Each with Try scopes), and D (VM queues with error handlers) are incorrect because they either don’t support parallel processing, lack centralized rollback orchestration, or are designed for reliability rather than distributed transaction management.
References:
➥ MuleSoft Documentation: Scatter-Gather (docs.mulesoft.com) – Describes parallel processing of routes and its use in orchestrating distributed transactions like the Saga pattern.
➥ MuleSoft Documentation: Saga Pattern (docs.mulesoft.com) – Explains the use of compensating actions for sequential rollbacks in distributed systems.
➥ MuleSoft Documentation: Parallel For Each and VM Connector (docs.mulesoft.com) – Clarifies their use for parallel or reliable processing but not for coordinated Saga-style rollbacks.
Two APIs are deployed to a two-node on-prem cluster. Due to a requirements change, the two APIs must communicate to exchange data asynchronously.
A. If the two APIs use the same domain, the VM Connector can be leveraged
B. The VM Connector is used to inter-applicationcommunication, so it is not possible to use the VM Connector
C. Instead of using the VM Connector use
D. It is not possible to use the VM Connector since the APIs are running in a cluster mode and each mode has it own set of VM Queues
Explanation:
In MuleSoft, the VM Connector enables asynchronous communication between flows or applications within the same Mule runtime or across a cluster. When two APIs are deployed to a two-node on-premises Mule cluster and use the same domain (a shared configuration context in Mule), they can leverage the VM Connector to exchange data asynchronously via VM queues. In a cluster, VM queues are automatically synchronized across nodes, ensuring reliable message delivery between APIs. MuleSoft’s documentation on the VM Connector (Mule 4) confirms that it supports intra-domain communication within a cluster, making it suitable for this scenario as long as the APIs share the same domain.
❌ Incorrect Answers:
❌ B. The VM Connector is used for inter-application communication, so it is not possible to use the VM Connector
This statement is incorrect because the VM Connector is not limited to inter-application communication. It can be used for both intra-application (within the same Mule application) and inter-application communication (between applications in the same Mule runtime or cluster) when applications share the same domain. In this case, the APIs are in the same cluster and can share a domain, allowing the VM Connector to facilitate asynchronous communication. MuleSoft’s VM Connector documentation clarifies its use for both intra- and inter-application messaging within a Mule runtime or cluster.
❌ C. Instead of using the VM Connector use
The
❌ D. It is not possible to use the VM Connector since the APIs are running in a cluster mode and each node has its own set of VM Queues
This is incorrect because the VM Connector in MuleSoft is designed to work in cluster mode. In an on-premises Mule cluster, VM queues are synchronized across nodes to ensure consistent message delivery, even if each node maintains its own queue instance. This clustering support allows APIs on different nodes to communicate asynchronously via the VM Connector, provided they share the same domain. MuleSoft’s documentation on clustering and the VM Connector (Mule 4) explains that VM queues are cluster-aware, enabling reliable communication across nodes.
🧩 Additional Context:
In a two-node on-premises Mule cluster, APIs deployed within the same domain share a common runtime context, allowing them to use VM queues for asynchronous communication. The VM Connector’s cluster synchronization ensures that messages sent from one API on any node are accessible to the other API, regardless of the node it runs on, making it an effective solution for this use case.
🧩 Summary:
Option A is correct because the VM Connector can be used for asynchronous communication between two APIs in the same domain within a two-node on-premises Mule cluster. Options B (VM limited to inter-application), C (use
ℹ️ References:
MuleSoft Documentation: VM Connector (Mule 4) – Describes the VM Connector’s support for asynchronous communication within and across applications in the same domain, including cluster synchronization.
MuleSoft Documentation: Mule Clustering – Explains how VM queues are synchronized across nodes in an on-premises cluster for reliable messaging.
MuleSoft Documentation: Flow Reference – Notes that

Prep Smart, Pass Easy Your Success Starts Here!
Transform Your Test Prep with Realistic Salesforce-MuleSoft-Developer-II Exam Questions That Build Confidence and Drive Success!

Frequently Asked Questions
Anypoint Platform Development (25%): Building Mule applications using Anypoint Studio, managing connectors, and working with flows, subflows, and private flows.
API Design and Development (20%): Designing RESTful APIs with RAML, applying API-led connectivity principles, and managing API lifecycle through Anypoint Exchange.
DataWeave Transformations (20%): Writing advanced DataWeave scripts to transform, map, and manipulate complex data structures including JSON, XML, and CSV formats.
Error Handling and Debugging (15%): Implementing robust error handling strategies, using Mule debugger, and managing exceptions across synchronous and asynchronous flows.
Deployment and Runtime Management (20%): Deploying applications to CloudHub, Runtime Fabric, and on-premise runtimes, and monitoring performance through Anypoint Monitoring.
Time allowed: 120 minutes
Passing score: 70%
1+ year of hands-on experience building integrations with Anypoint Platform
Prior completion of the MuleSoft Developer I certification
Strong proficiency in DataWeave 2.0 and API-led connectivity design patterns
Familiarity with CloudHub deployment, Runtime Manager, and Anypoint Monitoring tools